The blockchain in historical perspective
Accounting ledgers came before coinage and even writing. They're a core enabling technology for all complex human civilizations.
A few months ago, I started working on a less technical approach to explaining why the distributed ledger technologies that underly cryptocurrencies are a Big Deal of world-historic proportions. This was for a different outlet, and I ended up abandoning it to work on other stuff. You can see that I stopped as I was getting to the good parts — the next sections were on one-way hashes and digital signatures. If there’s some demand, I may continue it and add those sections.
The ledger in antiquity
In the ancient Sumerian hymn entitled, “House, Furious Storm of the Cosmos,” the underworld goddess Nungal holds in her hand a “tablet of life” that contains the name of every human, along with a record of their good and bad deeds. This is the first known appearance of a mythological archetype that comes up in many world religions: that of the deity who keeps a ledger of each person’s activity throughout the course of their life, with every action categorized as either good or bad.
Nungal’s tablet is one of many clay ledgers and records that populate Sumerian myths, and by the time it shows up in the historical record, the clay transaction ledger was already the product of thousands of years of technological evolution.
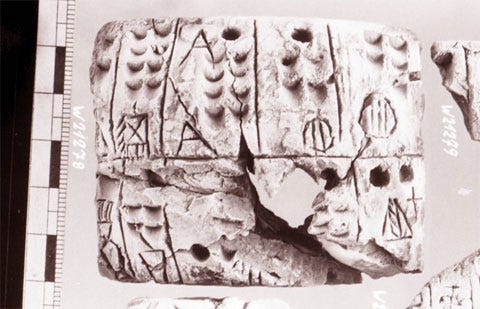
Jane Gleeson-White’s history of accounting, Double Entry: How The Merchants of Venice Created Modern Finance, tells the story of how the very technology of writing itself initially grew out of a distributed accounting mechanism involving a variety of shaped clay tokens. Different shapes represented different types of commercial goods that changed hands, and collections of these shapes were sealed into clay containers as an immutable, after-the-fact record that a transaction had taken place.
Historian Denise Schmandt-Besserat describes their usage this way:
Ca. 3500, the proliferation of token shapes and markings reflected the multiplication of commodities manufactured in urban workshops. Triangular shapes stood for ingots of metal; series of disks bearing on their face various numbers of parallel lines stood for various qualities of textiles and paraboloids for garments. Quantities of beer, oil, honey were shown by tokens in the shape of their usual containers. There is no evidence that tokens were used for trade. Instead they were central to administration.
These shapes were later pressed upon the outside of the containers so that the imprint would make it easy to read the contents of the container at a glance. Then the containers were flattened out into tablets, and the 3D clay tokens were dispensed with entirely, represented by geometric 2D markings that stood in for corn, oil, wheat, livestock, and other traceable goods. These transaction ledgers, then, were the earliest form of written communication, and other forms of written communication evolved from them.
Accounting ledgers not only predate writing, but they also predate money and coinage. It is the accounting ledger that’s the earliest abstract representation of an exchange of economic value, not the monetary token as a medium of exchange (i.e., money as a more convenient substitute for barter, which is how most popular but incorrect accounts of the evolution of money have its origins).
The transaction ledger, then, is the genesis of the media revolution that gave rise to urban civilization at the dawn of human history. From Sumer, to Babylon, to ancient Egypt, to Greece, and across the ocean in the great Mesoamerican empires, every civilization has filled its temples with accounting ledgers, genealogies, inventories, and rolls, all rendered in tablets, scrolls, books, beads, and knotted string.
Double-entry bookkeeping
Some of the earliest major advances in mathematics can be fairly categorized as user experience improvements — Arabic numerals, mathematical operators (i.e., plus, minus, and equals signs), and derivative notation are widely recognized examples of how just writing math out in a more accessible format unlocks new possibilities for discovery and innovation.
Double-entry bookkeeping is another, less widely appreciated user interface technology that has enabled a whole universe of accounting, banking, and corporate structure possibilities. Despite its relative obscurity outside of accounting circles, it’s one of the critical advances that gave us global trade in the Renaissance era and all modern finance.
Before the widespread introduction of double-entry bookkeeping in 15th century Vienna, accounting ledgers were simple, single-column lists of spending and income entries all mixed together. This was useful for providing a basic historical record of a household or firm’s economic activity, but you couldn’t really do much with it.
Single-entry ledgers are limited because each entry doesn’t explicitly spell out all the information needed to fully describe the transaction that the entry is supposed to represent. A transaction is a transfer of value from one party to another — from a sender of funds to a receiver of funds.
Look at the single-entry ledger example above and think about who (or what) the sending and receiving accounts are for each entry. Presumably the entry, “Butcher: $100” describes a payment to a butcher for some meat, probably paid out of some cash account for daily expenses. Likewise, “Art supplies: $100” describes payment to a store for the purchase of some art supplies, out of some business account if the person is an artist, or out of a cash spending account if they’re a hobbyist. “Rental income” sounds like income paid into an account from the rental of some property, but did it go into cash or into some dedicated savings account? “Loan to Alice” is obviously a loan of $20 from some account to someone named Alice, but from where?
This confusion arises in single-entry systems because each entry in an accounting ledger represents a two-sided transaction — from one person or account to another person or account (Even in the case of payment from multiple accounts to multiple parties, the transaction is still two-sided in that money still goes from somewhere, to somewhere.) But the single-entry ledger records only one side of a transaction, leaving the other to be inferred from context.
Double-entry bookkeeping’s key innovation is to explicitly show both sides of a transaction by recording each transfer of value twice — one entry to show where the funds in the transfer came from, and a corresponding entry to show where they were sent to. Hence the term “double-entry” — because for each transaction, there are two ledger entries,
There’s a second user experience innovation that goes along with the two-entries-per-transaction presentation, which makes the entry pairs easy to scan and total. Double-entry ledgers split the “amount” column into two columns: debits and credits. This way, each entry is easily categorized as either the credit or debit side of a transaction by placing the amount in the correct column. The two sides of each transaction always net out to zero.
The result is a nicely laid out table where the flow of funds can be quickly and reliably traced, and assets and liabilities can be visually scanned and easily totaled and balanced. Because assets and liabilities can be easily balanced, it’s far easier to spot accounting mistakes. And this ability to spot mistakes and errors makes double-entry better for auditing a company’s books to spot fraud or waste.
Protocols and Complex Organizations
Double-entry bookkeeping is more than just a user experience advance. Insofar as it has been accompanied by a set of standard ledger formatting rules and accounting conventions, it also represents the development of a protocol that accountants can easily interpret and use.
It’s worth taking a moment to unpack what a protocol is, at least as the term is used in computing. Because after we get through the historical background, we’ll jump right into the world of protocols, standards, and data formats in order to talk about Bitcoin.
Protocol basics
The term “protocol” has a number of definitions, even in computing, but this one from Britannica is good enough to get us started:
Protocol, in computer science, a set of rules or procedures for transmitting data between electronic devices, such as computers. In order for computers to exchange information, there must be a preexisting agreement as to how the information will be structured and how each side will send and receive it.
The two most basic elements of a protocol, then, are as follows:
A well-defined data format for structuring information
A set of agreed-upon rules for doing things to and with the information that’s structured in that format — i.e., create/read/update/delete actions, validation, transmission, etc.
A protocol lets you build new abstractions on top of structured information — not just technical abstractions, but social abstractions. As we’ll see when we get to the Bitcoin protocol, protocols are powerful tools for enabling us to coordinate the actions of humans and machines at a scale.
Indeed, the power of protocols is even evident in the animal world. The honeybee’s famous waggle dance is a communication protocol that lets other bees know precisely where to find nectar. As such, it’s a key enabler of the larger unit of bee organization that is the hive.
Double-entry as a protocol
Without a common set of accounting standards, each company might keep its books in an internal format that’s not readily intelligible to someone outside the company. An outsider who comes in has to learn a bunch of house rules in order to make sense of the books.
But with a standardized data format and a set of conventions for interpreting that format — i.e., with a common protocol — any accountant who knows the rules can open any set of books and make sense of them. Furthermore, they can safely add new entries, or go back and check old entries for errors.
The basic double-entry ledger format has the beginnings of a protocol, and it was later developed into a full-blown protocol by the introduction of rules around what kinds of accounts are customarily debited to vs. what kinds are credited from, rules for balancing the ledgers, and important facets of accounting practice.
This protocol enabled the development of an independent class of accountants, with their own guild, practices, and rules. The resulting openness and reliability of standardized accounting practices formed a foundation of trust and transparency on which were built publicly traded companies, capital markets, complex derivatives, and all the other innovations of modern finance.
Security, Trust, and Power
As big of an advance in security and correctness as double-entry bookkeeping is, it’s still the case that anyone with physical access to a ledger can potentially tamper with its records, thereby changing the story it tells about the past and the totals associated with its accounts.
If a thief or a scammer can find a way to erase ledger entries or write over them, or to replace an entire collection of records with a carefully doctored fake, then even the most scrupulously maintained set of accounting records can’t be relied on. To be reliable and worth using, a ledger must be made secure from malicious alteration — or ideally, from alteration of any kind other than adding a new record.
The ideal ledger
The ideal accounting ledger is chronologically ordered and append-only. That first quality — chronological order — is straightforward, and it simply means that ledger’s transactions are recorded and presented in the order that they took place — or, as close to that order as is feasible. If you spent $100 at the butcher and then stopped by the art supply store afterward for a $20 purchase, then the butcher shop transaction should come before the art supply transaction in the ledger.
If a ledger is append-only, then the only way to change it is to add new transaction records to the end of it. You shouldn’t be able to update or delete existing records, so if you need to correct a previous entry then you’d have to append a new entry that adjusts the totals in the relevant accounts so that they square with reality. When this append-only rule is enforced, the ledger’s record of the past is always the same, and everyone who uses it can ensure that it has not been secretly altered.
Preventing and detecting fraud
There are only a few ways to defend a document of any kind against tampering, each of which corresponds to a computing concept we’ll cover later:
Immutability: Write the information into a permanent, unalterable medium (e.g., fired clay).
Checks: Seal the document inside a container, so that any tampering can be detected by checking the seal. (A document secured by this approach isn’t so much tamper-proof” as it is “tamper-evident,” i.e. you haven’t stopped the tampering, only made it reliably detectable it after the fact.)
Custody: Store the document in a secure location, where only certain people have access (e.g., a temple or a royal vault).
At various times throughout history, people have tried one or more of these approaches — usually in combination with one another. The ancient, clay token records we met in an earlier lesson, for instance, combined all three — hard clay tokens were stored securely inside a clay container (called an “envelope” by archaeologists), and these containers were deposited in a centralized, secure location.
That third option — custody in a secure, access-controlled location — is perhaps the most commonly used means of securing an important ledger or body records against malicious tampering. But this approach has two important downsides: it requires trust in authorities and individuals, and (relatedly) it both depends on and perpetuates the centralization of power in a single custodial entity.
Trust and stakeholders
The first and most obvious problem with the secure location approach is that definitions of “secure” vary depending on factors like who owns the ledger, who owns the location, who might benefit from fraud, and many other incentives and power dynamics.
For instance, what if one of the people with access to the ledger is corrupt, or holds a grudge against someone whose finances could be affected by malicious tampering? Or, what if the institution charged with securing the ledger — a public entity like a state or temple, or a private entity like a firm — is subject to a set of incentives that makes it an unreliable custodian for some of the accounts it’s charged with keeping track of?
Central to all of the problems above is a deeper issue: trust. Whoever has physical access to an official ledger of record must be trusted by every party whose fortunes depend on that ledger’s accuracy.
Note: Anyone who depends on the integrity of a set of records, but who may or may not have custody of that ledger, can be usefully termed a stakeholder. This isn’t some standard terminology, but the concept of multiple parties who share a ledger and who have a stake in that ledger’s integrity will come up often as these lessons progress, so it’s worth giving it a name.
All the stakeholders in a shared ledger have to trust everyone with access to that ledger, and they also have to trust the custodial process or institution that grants such access. That’s a lot of trust in multiple directions, and often among parties that may not like each other or really want to trust each other, so it’s no wonder things so often go awry.
Custody is power
As we saw in the example of the Sumerian gods with their clay tablets, to hold an important ledger is to hold power — often not just figurative but literally, in one’s very hands. Generally speaking, whoever has custody of an important body of records has a form of power over every stakeholder who relies on those records and their integrity — whether those records are of assets, debts, tax rolls, physical addresses, etc.
Throughout history, the centralization of power required to support a single, authoritative, access-controlled repository of records for a vast number of stakeholders has been a fundamental feature of all forms of human organization at scale. Empires have lists, rolls, and archives of many kinds; banks have account ledgers; FaceBook has a users table. To custody these critical records is to have power, almost definitionally so. This is why, when we have a choice in the matter (we often don’t!), we give that power only to authorities we trust.
But what if we could have a ledger that’s not under the control of a central, custodial authority? What if access to that ledger could be managed by some form of group consensus that would prevent any one party — a person, company, government, cartel, or other group — from being able to alter the records without the consent of the other stakeholders? What if the stakeholders weren’t required to trust each other or anyone else in order to rely on the integrity of the ledger?
Believe it or not, fairly recent advances in an area of mathematics called cryptography have made such an arrangement not only possible but a reality. This new math has the potential to bring about social changes far more sweeping than double-entry bookkeeping. By freeing the ledger from its longstanding need for centralized custody and control, it represents a fundamental innovation in the ancient technology at the heart of all of humanity’s vehicles for collective decision-making and action.







FWIW - I'd be interested in the follow ups you mentioned.
Beautifully written. Looking forward to the next sections.